Welcome!
To the International Cybersecurity Research Focus at the IFSH.
Scientific Research on Cyber & Cognitive Conflict
Deepen your understanding of global cyber conflicts and their impact on security and politics.
Knowledge Transfer & Policy Work
We work to raise awareness, inform public opinion, and cooperate closely with policymakers and stakeholders.
Annual “Shaping Cybersecurity” Conference
We co-organize yearly conference on cybersecurity, bringing together international experts and policymakers.

News
-

Regulating Spyware Hubs: A Threat to Privacy and Democratic Control
-

Lena and Mateusz published an article in the newspaper “Praxis der Wirtschaftsinformatik”
-

Has Cyber Changed the Game?
-

Political Tech Summit
-

ICS activities in the second half of 2025
-

We are hiring!
-
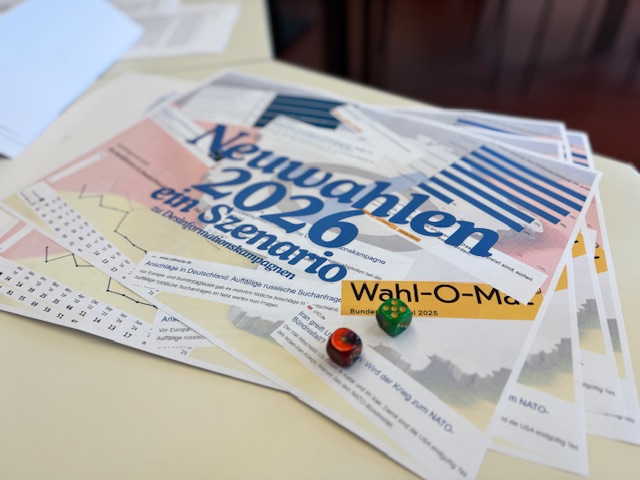
Defending democracy against foreign influence campaigns: A wargaming exercise
-
Webinar with Cyprus institutions
-

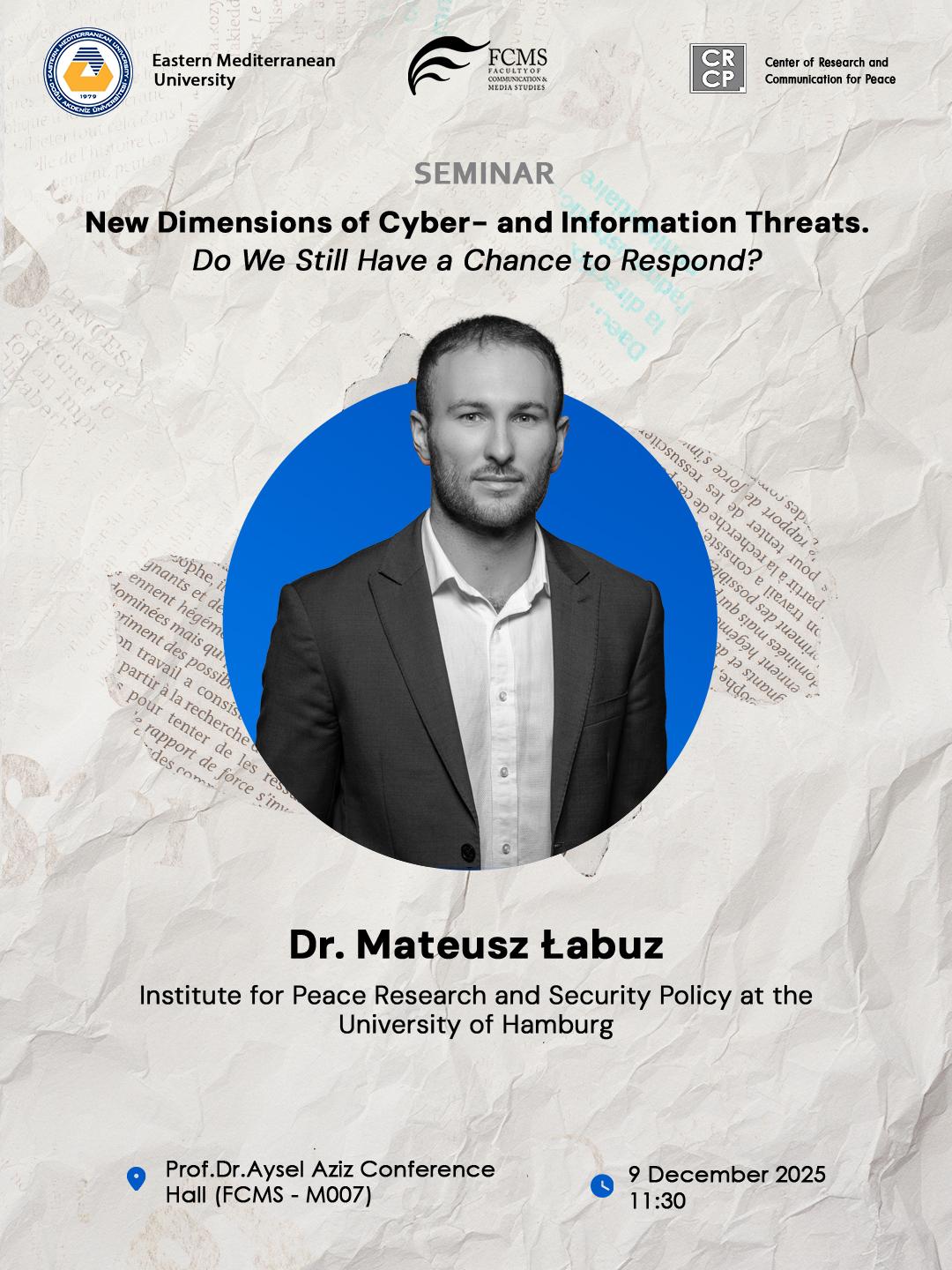
Mateusz as a speaker at the GIZ conference
-
Mateusz co-authored book
-

Matthias joins the BSI conference advisory board
-

PROTEKT – Roundtable Espionage & Zeitenwende
Research Topics

Cyber Conflict
Cyber conflict & the use of offensive cyber operations or active cyber defence as an element of International Relations. Governance of the cyber domain: cyber norms, confidence building measures and international law.

Cyber-Security & Strategies
Cybersecurity & cyber defence best-practices: vulnerability disclosure, cyber ranges, bug bounties and the evolution of security controls. Peace and security implications of the cybercrime ecosystem & ransomware. Analysing cyber strategies of allies and adversaries.

Hybrid Threats & Information Warfare
Information warfare, cognitive threats, memetic warfare and the use of synthetic media to influence democracies.
Subscribe to our Newsletter

Cyber & Cognitive Conflict Compass (C4) Substack
Weekly update on cyber and information warfare events around the globe, cyber-policy developments, new academic papers, and noteworthy IT-security news. Hosted via Substack.