China’s Industrial Espionage Against the U.S. Defense Sector (2000–2022)
In 1999, the U.S. House of Representatives released what became known as the Cox Report, concluding that China had acquired data on sensitive U.S. military technologies such as thermonuclear weapons through espionage and covert acquisition networks. The core concern was clear: China was systematically attempting to narrow the technological gap with the United States.
More than two decades later, that objective remains. What has changed is the operational environment. The digitization and the expansion of cyberspace have transformed the tools available for industrial espionage. The key question of this blog is therefore not whether China engages in industrial espionage against the U.S. defense sector, but whether cyber espionage has fundamentally altered how this competition unfolds.
From Conventional to Cyber Espionage
Traditional industrial espionage relies on human intelligence (HUMINT), physical acquisition and to a lower extent also signals intelligence (SIGINT). Chinese activities historically involved both civilian and military actors. On the civilian spectrum, the Ministry of State Security (MSS), established in 1983, conducts foreign intelligence operations through diplomatic, academic, and commercial channels, while on the military side the PLA’s former Second and Third Departments were responsible for HUMINT and SIGINT prior to later reforms.
Programs such as the “Young Thousand Talents” initiative and the “863 Program” (active until 2016) illustrate how knowledge acquisition was embedded within broader modernization goals. China’s industrial espionage has been closely linked to its effort to sustain economic growth, avoid structural stagnation, and narrow technological gaps, particularly in strategically sensitive sectors such as aerospace, electronics, and advanced optics. In the defense domain, the objective is clear: reduce technological inferiority and avoid strategic disadvantage in potential contingencies, especially with the United States.
These conventional methods depended on recruitment, inducement, and physical access. However, they were and are costly, risky, and limited in scale.
Cyber espionage changed that equation. As defense contractors digitized design files, simulation data, and internal communications, remote intrusion became possible. Campaigns such as “Titan Rain” (2003–2006), attributed to PLA-linked actors, marked an early turning point. Instead of cultivating insiders, attackers penetrated networks remotely and extracted large volumes of data. Later operations attributed to APT41 reportedly targeted dozens of firms simultaneously.
Cyber espionage introduced persistence within networks, remote access without physical presence, and large-scale data exfiltration which expanded both the scale and scope of industrial intelligence collection.
Methodology
Espionage is inherently difficult to measure. Undetected cases remain unknown, and reported incidents represent only a subset of actual activity.
The empirical basis of this analysis is the CSIS survey of Chinese espionage cases in the United States since 2000. Because the CSIS dataset does not systematically differentiate between industrial and non-industrial espionage or between cyber and conventional methods, a new dataset was constructed.
Each case was manually coded according to:
- year of activity ii) method (cyber or conventional) iii) espionage type (industrial vs. other) iv) victim type and sector targeted (civilian or defense)
Cases beginning before 2000 or unrelated to industrial espionage were excluded. The result is a systematically coded subset of the CSIS data, enabling time-series analysis of Chinese industrial espionage against the U.S. defense sector between 2000 and 2022.
Empirical Trends
The dataset must be interpreted cautiously. Observable trends may partly reflect improvements in detection and reporting as well as counterintelligence efforts or sanctions. It captures visible cases, not total activity.
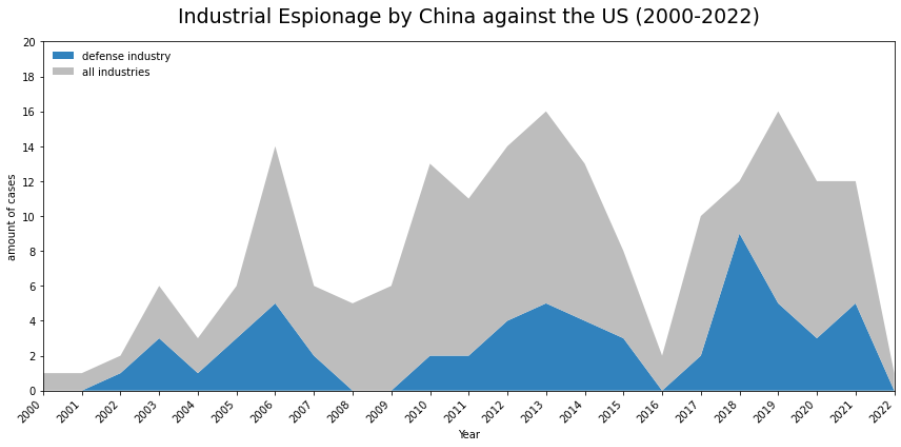
Despite these limitations, three patterns stand out.
First, a Long-Term Upward Trend.
Publicly reported Chinese industrial espionage cases show a pronounced upward trajectory from 2000 onward, intensifying after 2013.1 According to CSIS, approximately 69 percent of all documented Chinese espionage cases occurred after Xi Jinping assumed office.
This concentration aligns with China’s intensified pursuit of technological self-reliance, particularly following the 2006 Medium- and Long-Term Plan for Science and Technology Development. CSIS attributes part of the post-2013 increase to centralization and strategic alignment of espionage activities under Xi’s reforms.
Second, the 2016 Dip.
Reported cases decline sharply in 2016 before rebounding in 2017. This anomaly corresponds with the 2015 U.S.–China agreement to curb state-sponsored commercial cyber espionage. While espionage did not cease, the temporary decline suggests operational calibration, particularly in cyber activity—in response to diplomatic pressure.
Third, cyber overtakes conventional methods.
The most significant structural shift concerns method. In the early 2000s and mid-2010s, conventional and cyber methods coexist in comparable proportions. After roughly 2017, cyber espionage clearly dominates publicly reported defense-related cases.
Cyber activity shows a steady upward trend, interrupted only in 2016. Between 2017 and 2021 in particular, cyber operations account for the majority of visible defense-related espionage cases.
Conventional industrial espionage, by contrast, does not display a comparable structural transformation. The large decisive methodological change occurs in the cyber domain.
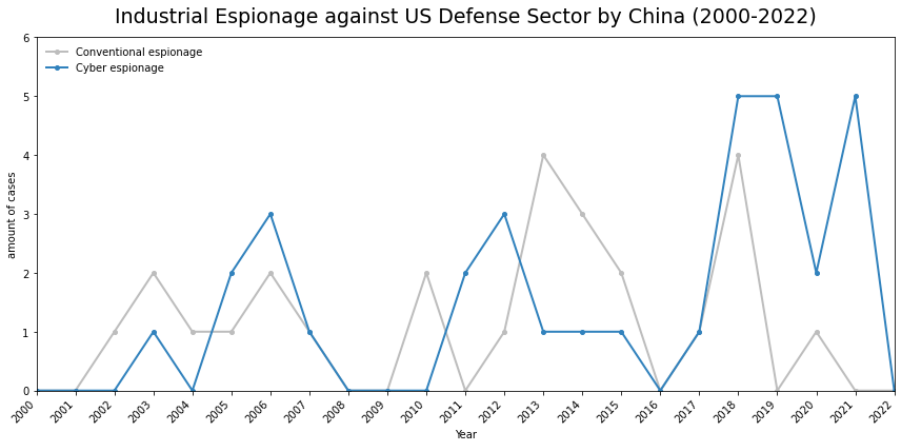
Sector-specific factors reinforce this pattern. Early export controls on military aviation technologies and persistent concerns about technological inferiority appear to have shaped targeting priorities. Cases such as Su Bin’s coordination of cyber theft related to the F-22 and F-35 programs illustrate how major U.S. defense advances function as focal points for collection efforts.
Taken together, the data indicates both quantitative growth and qualitative transformation: cyber increasingly dominates China’s industrial espionage against the U.S. defense sector.
Why Cyber Became Dominant
Cyber dominance is not accidental. It results from several reinforcing factors that affect industrial espionage overall but become especially decisive when targeting highly securitized defense contractors.
Cost and Scale: Conventional HUMINT operations are resource-intensive and risky as the recruitment of insiders or infiltrating a spy into a defense company requires years of cultivation and financial incentives. It is furthermore operationally complex due to clearance systems, a strict compartmentalization and robust insider threat detection mechanisms – especially in the defense realm.
Cyber operations however, once capabilities are developed, allow the bypassing of human barriers by targeting network infrastructure instead of individuals and therefore allow the simultaneous targeting of multiple organizations at comparatively lower marginal cost. Campaigns such as “Operation CuckooBees” where APT41 exfiltrated data such as defense related blueprints from approximately 30 multinational companies in parallel, demonstrate this scalability.
- Plausible deniability: Exposure of human agents carries direct diplomatic and reputational costs. Arrested agents can confess, cooperate with prosecutors, and provide evidence directly linking operations to state sponsors. Cyber operations operate in a more ambiguous attribution environment. States can deny responsibility and contest evidence, lowering immediate political risks, a strategy which China has repeatedly employed by making counteraccusations and build up narratives of victimhood. Especially, the Snowden disclosures in 2013 provided China with a powerful rhetorical tool to counter U.S. accusations.
- Digital Opportunity Structures: As defense contractors digitized their operations, sensitive data moved onto networked systems and cloud platforms. At the same time, digital links to global suppliers increased the number of potential entry points for intrusion.
The early case of “Titan Rain” which targeted US military and aerospace systems between 2003 and 2006 revealed systemic weaknesses in early network security. Cyber dominance in espionage became feasible because the technological environment made it so.
- Breadth and Ecosystem Access: Conventional espionage often yields discrete artifacts. Cyber intrusions can expose entire development environments: design iterations, testing data, software repositories, and internal communications.
This broader visibility potentially enhances effectiveness regarding using the stolen data and information for the very own programs, especially in complex environments such as the defense aerospace sector where isolated technical documents provide limited insight.
Yet, as Gilli and Gilli argue, access to data does not automatically produce technological parity. Integration challenges and tacit knowledge remain critical constraints.
Cyber offers scale and breadth – but not guaranteed success.
Why Cyber Does Not Replace Conventional Espionage
Despite its dominance in reported cases after 2017, cyber has not eliminated traditional methods. Why?
- First, data exploitation is not automatic. Especially as industrial cyber espionage often prioritizes breath over precision. Large-scale exfiltration creates analytical burdens. Without sufficient absorption capacity, as well as the necessary analytical infrastructure, stolen data may not translate into operational gains as filtering and contextualization are necessary to successfully be able to integrate the findings into domestic production systems. They might even overwhelm innovation.
- Second, highly compartmentalized defense projects restrict what cyber intrusions can realistically access. To prevent digital exploitation, the most sensitive program data is often stored on air-gapped systems or within tightly segmented networks, deliberately isolated from external connectivity. As a result, cyber operations may yield large volumes of peripheral information without reaching the most critical project-specific material. Human sources, by contrast, can provide precision, contextual understanding, and targeted access. In highly compartmentalized defense environments, precision often outweighs scale, especially when the objective is to obtain program-specific data.
- Third, tacit knowledge and production expertise cannot be fully digitized. For instance, successfully developing a fifth-generation fighter or stealth bomber requires more than access to design files. It depends on mastery of manufacturing tolerances, composite material behavior, propulsion system reliability, and stealth coating performance – forms of experiential and process-based knowledge that cannot simply be extracted through cyber intrusion. Where material properties and production techniques are decisive, physical acquisition, reverse engineering, or smuggling therefore remains relevant.
The persistence of technological gaps in certain domains, as discussed by Gilli and Gilli, illustrates these limits. In the case of fifth-generation fighter aircraft, China has relied heavily on targeting information related to U.S. programs such as the F-22 and F-35 through cyber, as reflected in the CSIS data. Yet access to design-related information has not automatically translated into full performance parity, underscoring the constraints of data-driven acquisition in complex military systems.
- Finally, cyber access is inherently fragile. Once an intrusion is detected, vulnerabilities can be patched, phishing attempts more effectively identified, and employees better trained to recognize social engineering tactics. Early high-profile cases—such as the exposure of APT1—prompted substantial defensive investments within the U.S. defense sector. Cybersecurity spending among U.S. defense contractors reached approximately USD 36.9 billion in 2023 and is projected to rise to around USD 50 billion by 2028.
Human penetration, by contrast, can provide stable and sustained intelligence flows. A well-placed insider may continue to deliver targeted, high-value information on defense projects over extended periods, even as technical defenses evolve.
Overall, the empirical record suggests integration rather than substitution. Cyber operations map networks and gather bulk data; conventional methods refine targeting and fill critical gaps. Cases such as Su Bin’s coordination of cyber theft highlight this hybrid model.
Conclusion
Cyber espionage represents a qualitative expansion of intelligence collection. In China’s industrial espionage against the U.S. defense sector, it has clearly become the dominant method since the mid-2010s, fundamentally altering scale and speed of data acquisition.
Yet dominance does not equal replacement. Conventional espionage remains essential where precision, tacit knowledge, and highly compartmentalized information are involved. China’s approach is best understood as synergistic: cyber operations provide breadth and mapping of technological ecosystems, while human methods complement and refine these gains.
Cyber has changed the game – but it has not ended it. The balance between digital and conventional intelligence collection in the defense sector remains dynamic rather than completely converging toward a single model.
1 The apparent decline in cases toward the end of the observation period in 2022 should be interpreted cautiously, as there might be delays in reporting and further data may alter this picture.
Author: Florian Erdle